DPRK Hackers Use GitHub as C2 in South Korea Attacks
Fortinet says DPRK-linked attackers used GitHub as C2 in multi-stage attacks on South Korea, starting with LNK files and a decoy PDF.
Fortinet says DPRK-linked attackers used GitHub as C2 in multi-stage attacks on South Korea, starting with LNK files and a decoy PDF.

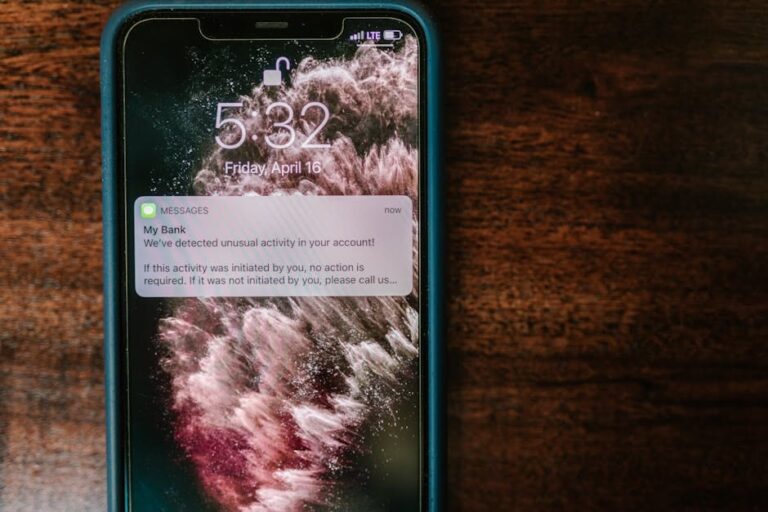
A suspected Iran-linked campaign used password spraying against Microsoft 365 tenants in Israel and the UAE across three March 2026 waves.

Qilin and Warlock ransomware groups used vulnerable drivers to disable more than 300 EDR tools. Here’s the timeline, technique, and defense angle.

LiteLLM’s supply chain attack showed how developer workstations can store reusable secrets, putting cloud access and AI tooling at risk.
This week’s security recap covers Axios tampering, a Chrome zero-day, Fortinet exploitation, and spyware activity that raised the pressure on defenders.